Architecture & Security Assessment for Critical Systems
Independent technical evaluation of existing applications and infrastructure to improve scalability, security posture, performance, and long-term sustainability across government and enterprise environments.

Comprehensive Technical Evaluation
Structured assessment frameworks designed to identify architectural gaps, security risks, and performance constraints.
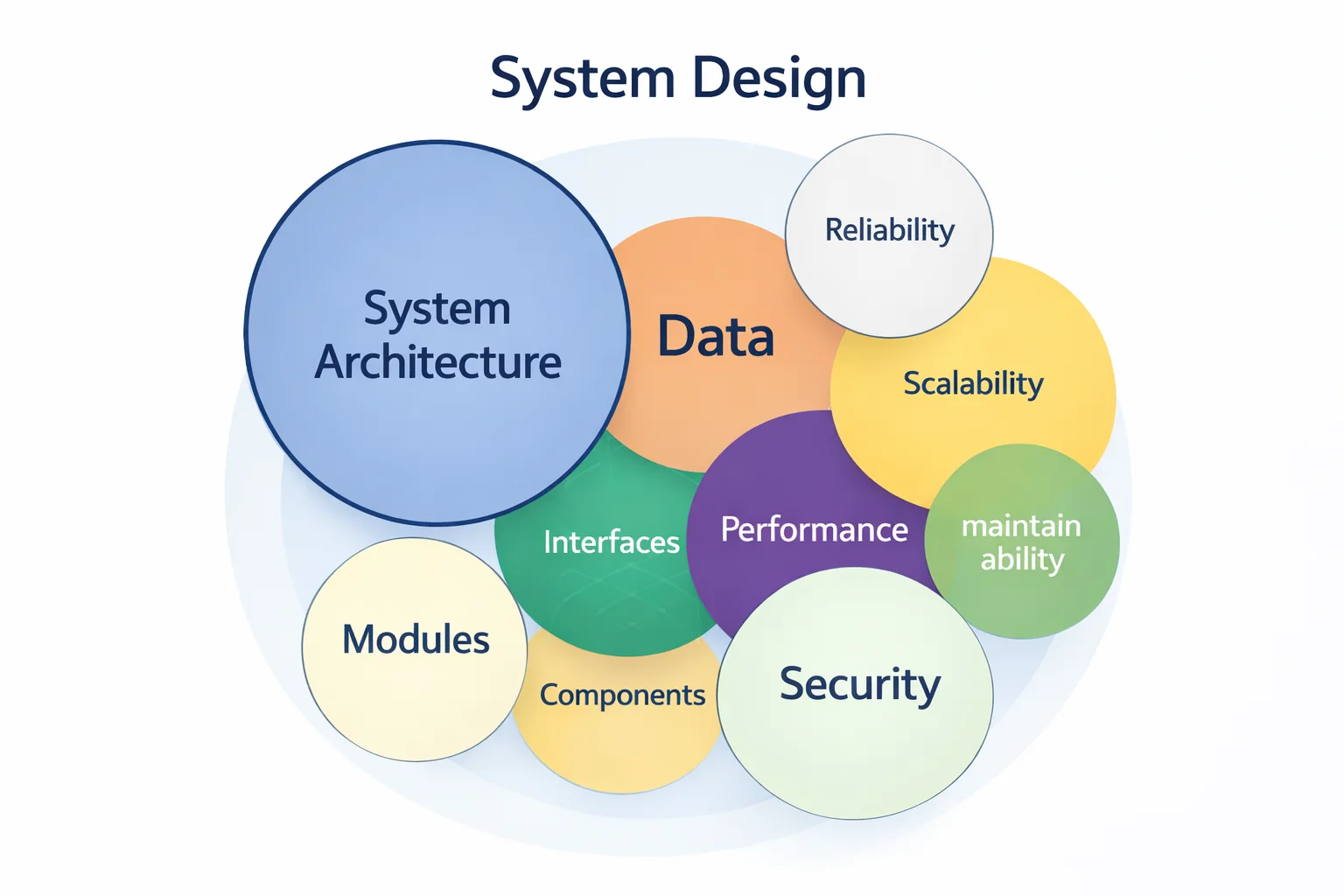
Application Architecture Assessment
Evaluation of system design, scalability readiness, modular structure, and long-term maintainability.
Codebase Structure Review
Scalability & Load Assessment
Dependency & Framework Analysis
Integration Architecture Review
Objective & Actionable Reporting
Every assessment concludes with a structured report outlining risk levels, priority actions, and practical improvement steps.
Risk Categorization Matrix
Clear prioritization of vulnerabilities.
Remediation Recommendations
Actionable technical guidance.
Scalability Readiness Assessment
Evaluation for future growth planning.
Security Hardening Guidance
Configuration and deployment improvements.
Performance Optimization Insights
Infrastructure and database tuning recommendations.
Governance Documentation Support
Compliance-aligned reporting structure.

Strengthened System Readiness
Improved reliability, reduced security exposure, and clearer governance alignment for mission-critical systems.
Identification of vulnerabilities before operational impact.
Architecture optimized for growth and higher user loads.
Audit-ready documentation and traceability controls.
Optimized infrastructure and database efficiency.
Aligned with Enterprise Best Practices
Assessments conducted using structured technical frameworks and recognized security guidelines.
OWASP Security Standards
Application vulnerability framework.
Architecture Review Models
Scalability and modular evaluation criteria.
Infrastructure Benchmarking
Environment configuration standards.
Performance Testing Tools
Load and stress evaluation frameworks.
Compliance Documentation Templates
Structured reporting format.
Continuous Improvement Planning
Long-term system sustainability strategy.